There are few things more tragic in this world than seeing a friend or family member suffer at the hands of some debilitating ailment or disease.
Such conditions rarely come up here in the Linux blogosphere, of course, but the past few weeks have been a rare exception. It was no physical ailment being discussed this time, however; rather, it was the sometimes crippling effects of "Microsoft Trained Brain Syndrome."
Yes, you heard that right -- Microsoft Trained Brain Syndrome, or MTBS, has recently become widely recognized as an ailment that affects a disproportionately large number of computer users today, and its effects are nothing if not debilitating.
Lost and Confused
"The problem is that people who have lived, worked, and played in a homogeneous Microsoft computing paradigm are lost and confused when they encounter a different paradigm,"
explained a blogger named Gene who apparently coined the term a couple years back on the ERA Computers & Consulting Technical Blog.
"These people have only seen the flawed Microsoft ideology for how computing systems should work and so have a difficult time with more elegant systems based on Unix,"
Gene continued. They see the Linux system with its own paradigm and ideology and try to force it into the only paradigm they know, which is Microsoft's.
"This will always cause the user problems," Gene pointed out.
Ignore Your Previous Knowledge
Indeed, it can be heartbreaking for those of us who use Linux to watch our loved ones stumble through today's computing landscape, effectively blinded by years of paying homage to Redmond.
What can be done? Well, as with so many conditions, victims must often begin by recognizing that they have a problem.
"Do not attempt to force preconceived notions and knowledge from a totally different computing paradigm onto Linux,"
Gene advised the unfortunate ones. "Ignore your previous knowledge from your Microsoft Trained Brain and start over with Linux as if you are a child getting a first exposure to computing systems. I guarantee this will help you in the long term."
By way of an extra incentive, "many of us wait to welcome you to our universe of heterogeneous computing," Gene added.
Debilitating Symptoms
Now, it's a simple fact that many of the victims of MTBS don't know they have a problem.
The condition received new attention recently, however, when it was discussed on a write-up in First Arkansas News. From there, it spread to PCWorld and beyond, making it patently clear to Linux Girl that it was time to get some tongues a-wagging down at the Broken Windows Lounge.
"MTBS is a chronic disease developed over a decade or more of doing things M$'s way," blogger Robert Pogson began. He proceeded to identify some of its symptoms:
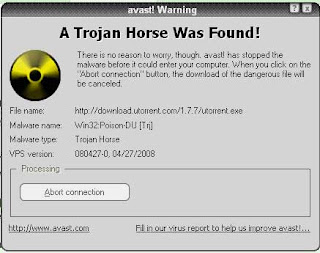
- "accepting slowing down, malware, BSODs, and re-re-reboots as normal;
- accepting products shipped with faulty software as the standard;
- accepting that a file can only be opened by the programme that created the file;
- accepting 'wait' and 'please wait' as normal when sitting in front of a computer capable of moving many gigabytes per second."
The path of infection, meanwhile, is "usually exposure to a monoculture of that other OS in homes, schools and offices," Pogson added.
The cure, however, "is a weekend with GNU/Linux running like a rocket on hardware discarded as slow with that other OS," he pointed out. "The cure is seeing 30 simultaneous users enjoying the experience of hardware that struggles with one user on that other OS."
A Widespread Problem
Similarly: "the core point is very true in that there are a lot of things Linux does _better_ than the competition, but it's often perceived as worse in these areas because people assume that the only way of doing things is the Microsoft or Apple way," Slashdot blogger David Masover agreed.
However, "this isn't always the case," he suggested. "It's far too easy to look at someone's legitimate complaint and say, 'this only bothers you because you're so used to Windows. You get used to it.'"
In addition, "'diagnosing' someone with a 'syndrome' -- even if it's accurate -- isn't the best way to get them to take you seriously," Masover pointed out.
In fact, MTBS doesn't affect only Microsoft users, consultant and Slashdot blogger Gerhard Mack asserted.
"The saying used to be that 'no one ever got fired for buying IBM,'" Mack noted. "People have a tendency to stick with what they consider safe, and it takes something large to force a change."
'What They Want Most Is to Be Right'
Indeed, "people make an emotional investment in their decisions that leads them to defend them even in the face of overwhelming evidence that they are wrong, or at least have made a suboptimal decision," Hyperlogos blogger Martin Espinoza opined.
For instance, "when Linux was coming up, the Windows-heads decried its free nature and defended Windows on the basis that nothing given away for free can be good," Espinoza explained. "Today they tend to fall back on FUD regarding patent licensing to defend their decisions, but in the end it is simply an attempt to maintain the apparent rationality of their world view."
The same force, in fact, "results in reelection of the incumbent in the vast majority of cases, even when voters claim to want change," he noted. "What they want most is to be Right with a capital R. In order for that to be happen, you must be wrong."
In short, "it's not about Windows, it's about selfish and self-serving decision processes," Espinoza concluded.
Linux Delusion Syndrome
Slashdot blogger hairyfeet took it even further.
"I will accept MSFT Brain syndrome if and ONLY if Linux geeks will accept they have LDS: Linux Delusion Syndrome,"
asserted hairyfeet, a self-proclaimed Windows fan. "It causes otherwise normal people to believe totally crazy things, like they can get home users to use CLI, or give up years of experience with apps they are happy with for frankly a third-rate experience."
To help their platform succeed, "LDS sufferers need to look at Apple for an example instead of their Unixy grandpa," hairyfeet added. "In iLand there is NO CLI, NO configuring, it is ALL GUI, it is ALL intuitive and simple."
'It's Only Worth What You Paid for It Syndrome'
Barbara Hudson, a blogger on Slashdot who goes by "Tom" on the site, saw it differently.
"I wouldn't say it's a Microsoft Trained Brain thing," Hudson told Linux Girl. "After all, people stuck with Microsoft in the changeover from Windows 9x to Windows xp, and they had to relearn a lot of things. And they're doing the same, to a lesser extent, with Windows 7."
Rather, the problem centers on the old "it's only worth what you paid for it" syndrome, Hudson suggested. After all, "most people, at some level, believe that money is the best indicator of quality."
What Linux needs to proliferate, then, is for someone "to create a fully GPL-compliant distro with a suggested retail price of (US)$259 for the home edition, $599 for the pro edition, $2,199 for the corporate edition, and $16,999 for the enterprise Enterprise Payment Security 2.0 Whitepaper from CyberSource edition, and then stick it on Pirate Bay," she explained. "People won't mind spending $70 on a second hard drive to 'test' their 'pirated' copy."
Not only that, but "they'll do their testing on recent machines," Hudson added -- "not some old piece of junk they have hanging around that will run so slow that they'll conclude, 'linux is the sux.'"
courtsey -technewsworld