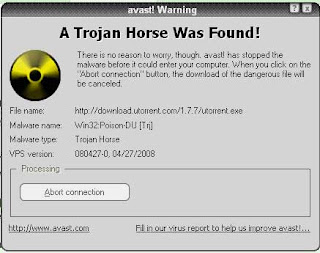
The Trojan horse still lives. Never download an unsolicited email attachment, as it may be embedded with the deadly Trojan virus, which could wreak havoc on your computer.
Recently in San Francisco, Uri Rivner, head of new technologies at RSA, the security division of EMC, said Trojan horse is a destructive program that masquerades as a benign application. It even puts online banking passwords at risk.
Rivner said Trojans are highly sophisticated, easy to use malware (malicious software) and don't cost much. Their distribution is also quite simple. The infection mechanism is very effective. It can get into your computer system if you go to a hijacked, but legitimate-looking website or if you are tricked into downloading a link or email attachment.
Once in the computer, it can give the malware creator complete remote control of your machine. The virus may sit dormant until you visit the website of a bank or a credit card company or other financial institution, whereupon it secretly records the passwords, account details and other confidential information.
A Trojan Virus can record every keyboard stroke of the user. The stolen details are then sent back to the Trojan operator, who uses them in online fraud scams like transferring money from banks.
Rivner says the two most dangerous Trojans are Zeus and SpyEye. Millions of computers across the world are infected by these Trojans. These two malwares are now merging. SpyEye is taking over Zeus operations, Rivner adds.
Rivner says cyber criminals know that it's hard to take on the bank's systems, so they attack the weakest link in the chain, that is, the online bank customers. The new Trojan virus can empty bank accounts without the owner knowing about the theft, as it shows him fake statements or gives him an illusion that everything is in order.
It's only when he goes to the ATM to collect cash or when he gets the hard copy of the bank statement that the reality dawns on him.
However, Rivner says it is relatively easy to protect against Trojan attacks by installing antivirus software and keeping it up to date. Users should keep their anti-spyware and firewalls set to the highest level.
But more importantly, computer users should be more circumspect when receiving an email or a download. "Even if you receive a link from a friend, be a little suspicious,"he cautions.
Local Money Mules
Many of the cyber criminals carrying out this type of fraud are located abroad, so they need a local money mule to send them the funds overseas. A mule is a person who allows his bank account to be used by fraudsters to transfer illicit gains to overseas accounts.A mule account is a legal bank account held by a real customer. He says many such mules are job seekers, who are promised handsome commissions in exchange for channelling funds overseas.
"Once recruited, the mule will receive the stolen funds in his account. He is then required to withdraw the funds and send them abroad, using a legitimate money transfer service. Often the mules are innocent victims. They believe they are working for a legitimate business,"says Rivner.
Rivner says banks are aware of this malware. They have put in place better authentication methods and defence mechanisms to keep out fraudsters. One of them is to send a tracker id number or code number to the online bank customer on his mobile phone via SMS.
It asks the customer to fill that number on the web page while transferring any amount through Net banking. So even if an attacker piggybacks on that session via the Trojan to make any fraudulent transaction, he can't finish the process till he has furnished the code number.
And under no circumstances will he have this crucial code number unless he has also stolen your mobile phone along with hijacking your web page. "So netbanking can be made safe," Rivner says.
No comments:
Post a Comment